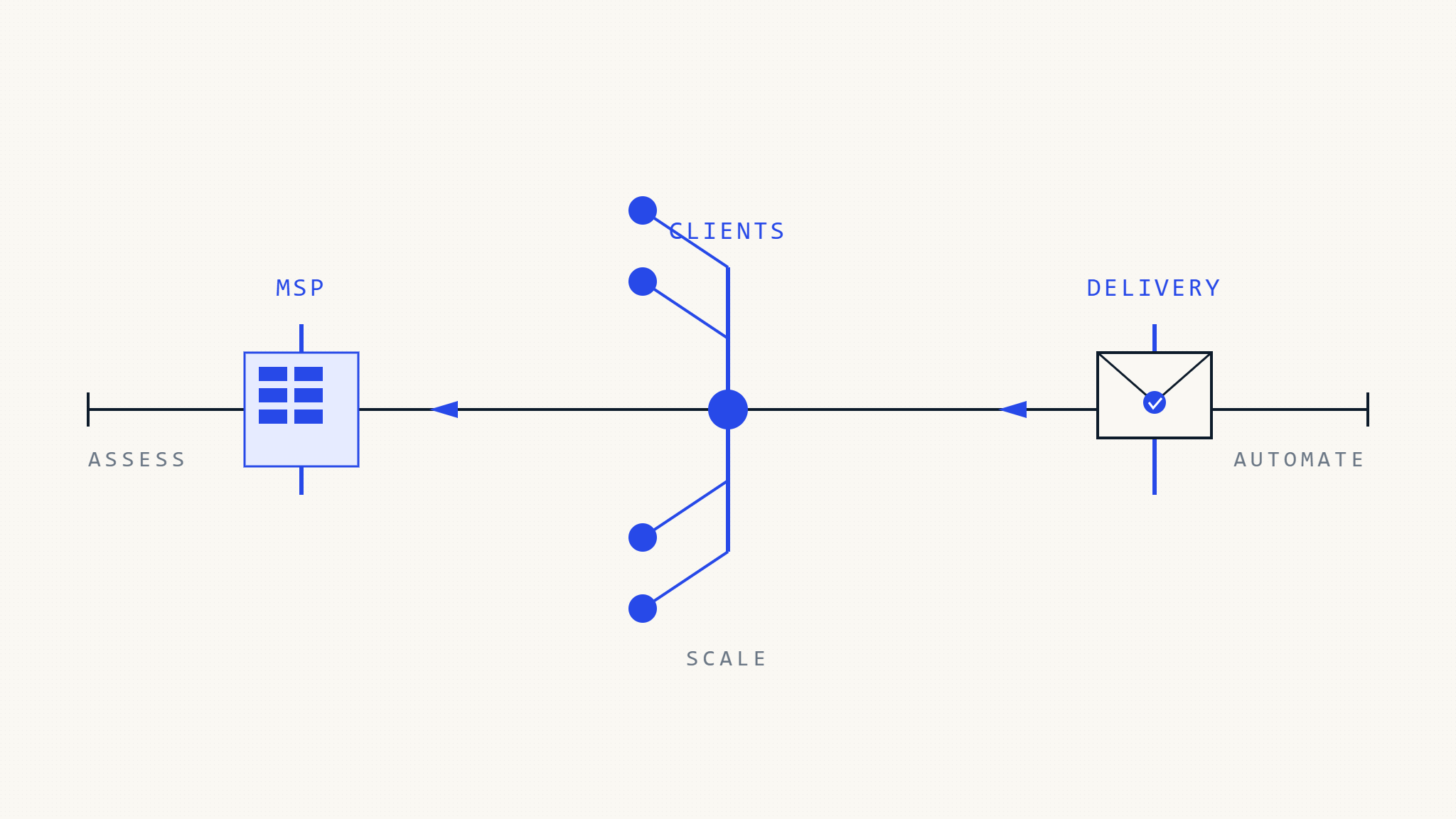
Managing email deliverability across dozens or hundreds of client domains requires specialized processes, tools, and strategies that go far beyond single-organization implementations. As an MSP, your clients depend on you to maintain their email reputation while protecting their domains from spoofing attacks—all while operating efficiently at scale.
This comprehensive checklist covers the essential strategies for managing email authentication across multiple clients, from initial assessment through ongoing monitoring and optimization.
I. Assessment: Understanding Your Multi-Client Environment
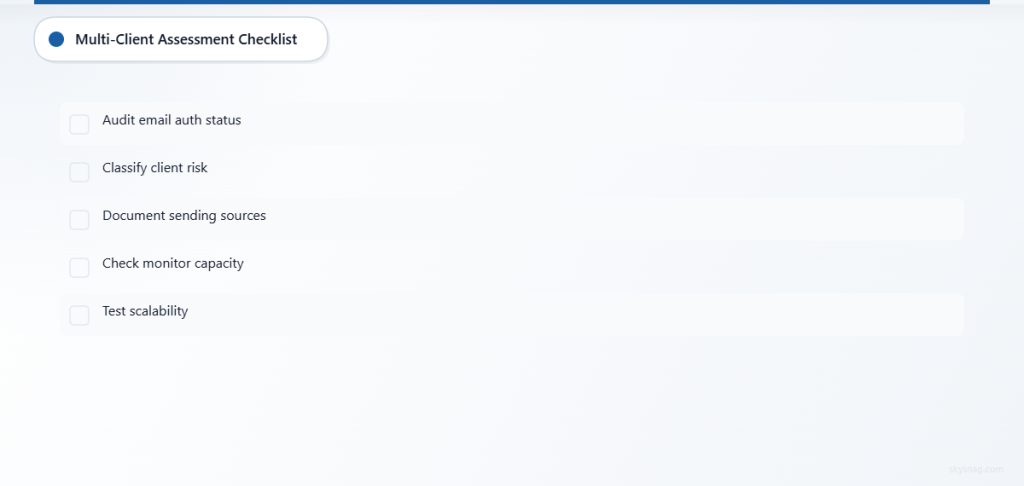
Client Portfolio Analysis
□ Audit existing email authentication status across all client domains
- Document current SPF, DKIM, and DMARC implementation status
- Identify domains with no authentication records
- Note domains using deprecated or problematic configurations
- Catalog third-party email services used by each client
□ Classify clients by email complexity and risk profile
- High-volume senders (marketing, e-commerce, SaaS platforms)
- Standard business users (office communications, basic marketing)
- Specialized industries with compliance requirements
- Clients using multiple email vendors or complex sending patterns
□ Document client-specific sending sources
- Internal mail servers and IP addresses
- Marketing automation platforms (HubSpot, Marketo, Mailchimp)
- Business applications (CRM systems, helpdesk software)
- Third-party services (payment processors, notification services)
Infrastructure Requirements Assessment
□ Evaluate centralized monitoring capabilities
- Current ability to monitor DMARC reports across multiple domains
- DNS management processes and access controls
- Incident response procedures for deliverability issues
- Reporting capabilities for client communication
□ Assess scalability of current processes
- Time required to onboard new client domains
- Manual vs. automated configuration management
- Ability to handle DMARC report volumes across all clients
- Resource allocation for ongoing monitoring and optimization
II. Actions: Implementing Scalable Email Authentication
Standardized Implementation Framework
□ Develop standardized SPF record templates
- Create modular SPF records that accommodate common sending sources
- Establish guidelines for SPF record length and DNS lookup limits
- Document approved third-party services and their required mechanisms
- Implement version control for SPF record changes
□ Establish DKIM key management procedures
- Standardize DKIM key lengths (2048-bit minimum)
- Create rotation schedules for DKIM keys
- Document key storage and access procedures
- Establish backup and recovery processes for DKIM keys
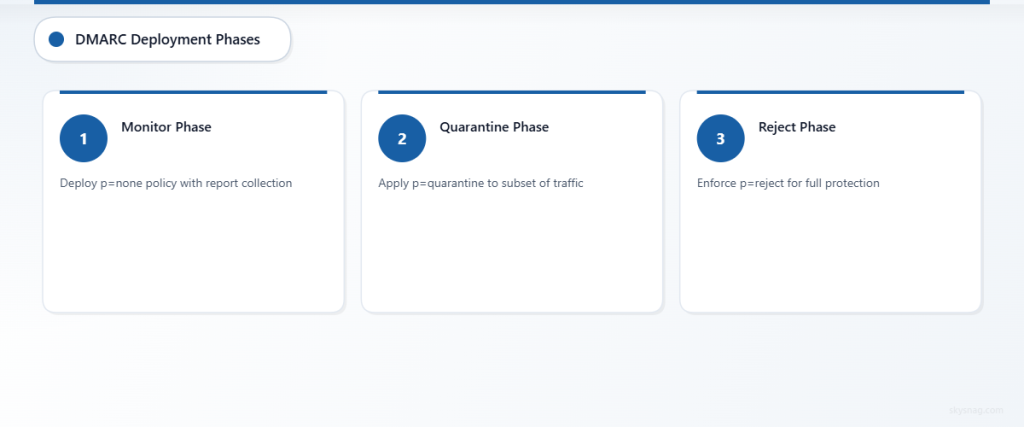
□ Design phased DMARC deployment strategy
- Phase 1: Monitor-only policy (p=none) with report collection
- Phase 2: Quarantine policy (p=quarantine) for subset of traffic
- Phase 3: Reject policy (p=reject) for full protection
- Define criteria and timelines for advancing between phases
Multi-Tenant Management Processes
□ Implement centralized DNS management
- Establish controlled DNS update procedures
- Create approval workflows for authentication record changes
- Document rollback procedures for problematic changes
- Implement change logging for audit and troubleshooting purposes
□ Create client communication protocols
- Standard notifications for authentication changes
- Regular deliverability health reports
- Incident communication templates and escalation procedures
- Educational materials about email authentication benefits
□ Develop service level agreements for email deliverability
- Define response times for deliverability issues
- Establish metrics for email authentication compliance
- Create clear responsibilities for client vs. MSP actions
- Document limitations and exclusions for complex scenarios
Compliance and Security Integration
□ Align email authentication with client compliance requirements
- Map email security controls to relevant compliance frameworks
- Document how DMARC enforcement supports client security objectives
- Integrate email authentication into security assessment processes
- Create compliance reporting templates that include email security metrics
□ Establish security incident response procedures
- Define triggers for email-related security incidents
- Create playbooks for domain spoofing attacks
- Document forensic analysis procedures using DMARC data
- Establish communication protocols during security events
III. Automate: Scaling Through Technology Solutions
Multi-Tenant DMARC Management Platform
□ Deploy centralized DMARC monitoring solution
- Implement automated DMARC report collection across all client domains
- Configure intelligent parsing and analysis of report data
- Set up automated alerting for authentication failures and policy violations
- Create customizable dashboards for different client needs
□ Automate policy recommendations and updates
- Use machine learning to identify legitimate vs. unauthorized senders
- Generate automated recommendations for DMARC policy progression
- Implement staged rollout capabilities for policy changes
- Create approval workflows that maintain client control while enabling efficiency
Integration and Workflow Automation
□ Integrate with existing MSP tools and workflows
- Connect DMARC management with PSA (Professional Services Automation) systems
- Integrate email deliverability metrics into client reporting dashboards
- Automate ticket creation for deliverability issues requiring attention
- Sync client domain inventories with email authentication monitoring
□ Implement automated onboarding processes
- Create standardized workflows for new client email authentication setup
- Automate initial domain discovery and authentication status assessment
- Generate client-specific implementation roadmaps and timelines
- Establish automated progress tracking and milestone reporting
Advanced Analytics and Reporting
□ Deploy predictive analytics for deliverability optimization
- Monitor sender reputation trends across client domains
- Identify patterns that predict deliverability issues
- Generate proactive recommendations for authentication improvements
- Track ROI metrics for email authentication investments
□ Create client-specific reporting and insights
- Generate automated monthly deliverability health reports
- Provide domain-specific insights and recommendations
- Create executive summaries for client stakeholder communication
- Implement real-time alerting for critical deliverability events
IV. Best Practices for Multi-Client Success
Operational Excellence
□ Maintain detailed documentation and procedures
- Document all client-specific configurations and exceptions
- Create troubleshooting guides for common deliverability issues
- Maintain change logs for all authentication record modifications
- Establish knowledge base for team training and continuity
□ Implement quality assurance processes
- Regular audits of client email authentication configurations
- Validation of DMARC report processing accuracy
- Performance monitoring of automated systems and processes
- Client satisfaction surveys specific to email deliverability services
Strategic Client Engagement
□ Position email authentication as a strategic security service
- Educate clients about the business impact of email deliverability
- Connect email security to broader cybersecurity initiatives
- Demonstrate ROI through improved delivery rates and reduced spoofing incidents
- Create upsell opportunities for advanced email security services
□ Stay current with industry developments
- Monitor changes in major email provider policies and requirements
- Track emerging authentication technologies and standards
- Participate in industry forums and maintain vendor relationships
- Update client strategies based on evolving threat landscape
Skysnag MSP/MSSP Comply provides the specialized multi-tenant capabilities MSPs need to efficiently manage email authentication across client portfolios. The platform’s centralized dashboard, automated policy management, and white-label reporting capabilities enable MSPs to scale their email deliverability services while maintaining the personalized attention clients expect.
V. Key Takeaways
Successful multi-client email deliverability management requires standardized processes, automated tools, and clear communication protocols. MSPs that invest in proper infrastructure and procedures can deliver superior email security services while operating efficiently at scale.
The key to success lies in balancing automation with client-specific needs, maintaining detailed documentation, and continuously optimizing processes based on performance data and client feedback. With the right approach, email authentication services can become a significant differentiator and revenue driver for MSPs.
By following this checklist and implementing appropriate automation tools, MSPs can provide enterprise-grade email deliverability services that protect client domains, improve email performance, and support broader cybersecurity objectives.